The new IoT security solution will be available as part of NetSTAR’s inCompass threat intelligence product.
NetSTAR has enhanced its inCompass® threat intelligence solution, amping up its cybersecurity capability to detect threats to IoT security.
As the world depends more and more on IoT devices, like smart TVs, wearables, home/ factory automation, manufacturing sensors, smart city/ utility sensors, and more, the threat potential to IoT security also grows.
IoT devices continue to deploy on an increasingly larger scale, and many have little — if any — protection from attacks. NetSTAR’s inCompass® enhancements improve its malware detection functionality.
Those improvements include a honeypot system using both real and emulated IoT devices and services to observe attacks. While an increase in short-lived malware and more complex attack patterns hamper conventional honeypot systems from detecting all threats, inCompass has more capabilities.
The new system enables detection of unauthorized attempts that traditional honeypot setups might miss. It can also execute more extensive, immediate threat countermeasure data.
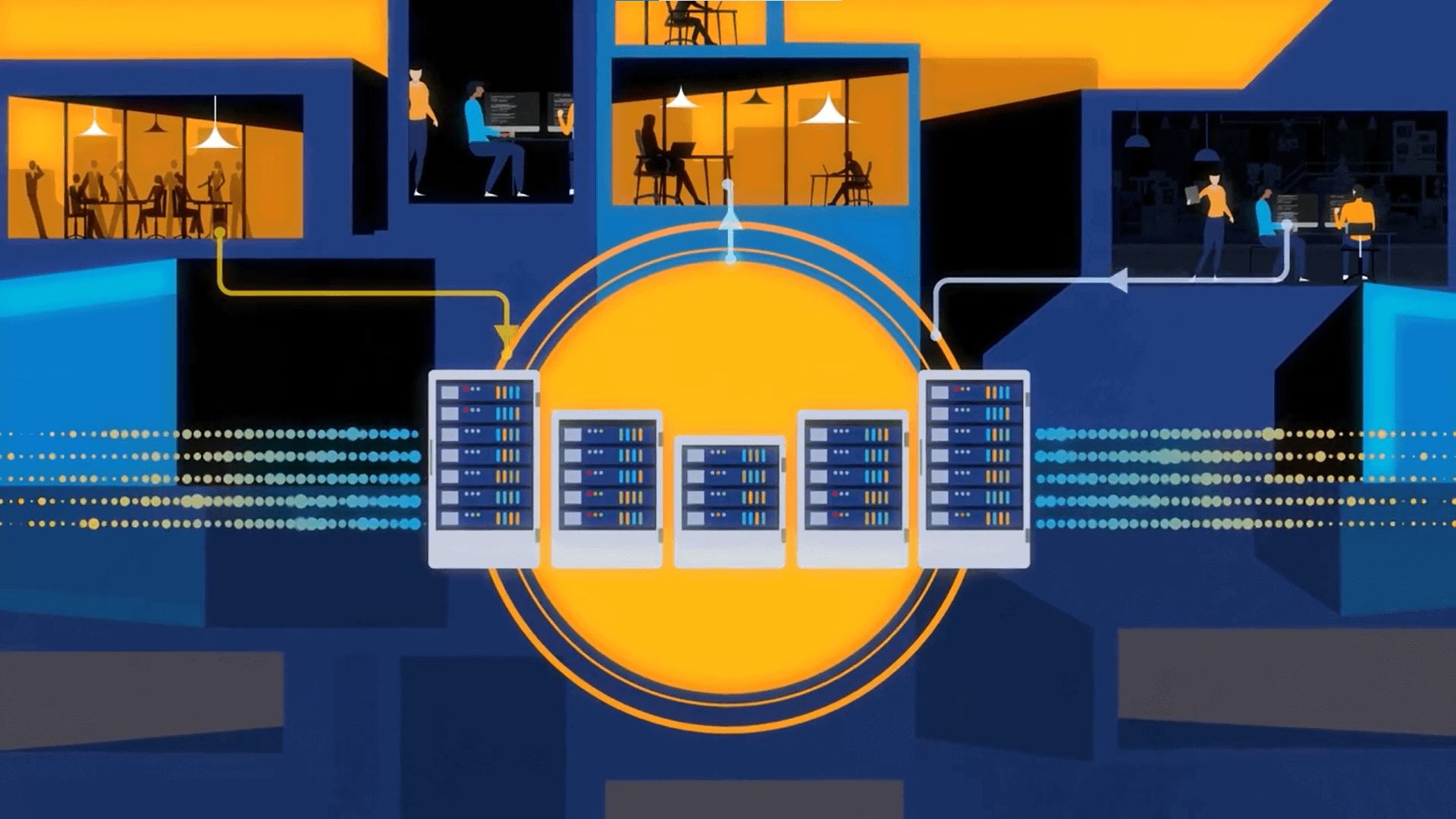
Daniel Ashby, SVP of NetSTAR, says: “NetSTAR is leveraging threat countermeasure data based on the IoT honeypot systems. We have multiple servers processing the honeypot system data, categorizing associated IPs as malicious, and updating our global inCompass® database so that our technology and telco partners have up-to-date visibility into these security vulnerabilities.”
Ashby says, “Our OEM partners use this intelligence to power their web filtering solutions, enhance their threat information capabilities, and create new network policies around IoT devices.”
NetSTAR’s honeypot system uses a large pool of IP addresses and multiple IoT devices to detect attacks along with the virtual environment to monitor attacks against ports. Researchers use Telnet, HTTP, downloads and remote connections to observe these short-lived attacks and identify IP addresses connected to botnet attacks.